Precision in Detection
and Response
Scale your security operations with an architectural approach to threat management. Eliminate noise, automate workflows, and reduce enterprise risk through systemic intelligence.
Live Monitoring
Sentinel Active Core
MTTD
1.2m
Reduction
94%
Orchestrated Remediation
Streamline the bridge between detection and resolution. Our collaborative workflow tools ensure every critical alert is tracked, assigned, and remediated with clinical precision.
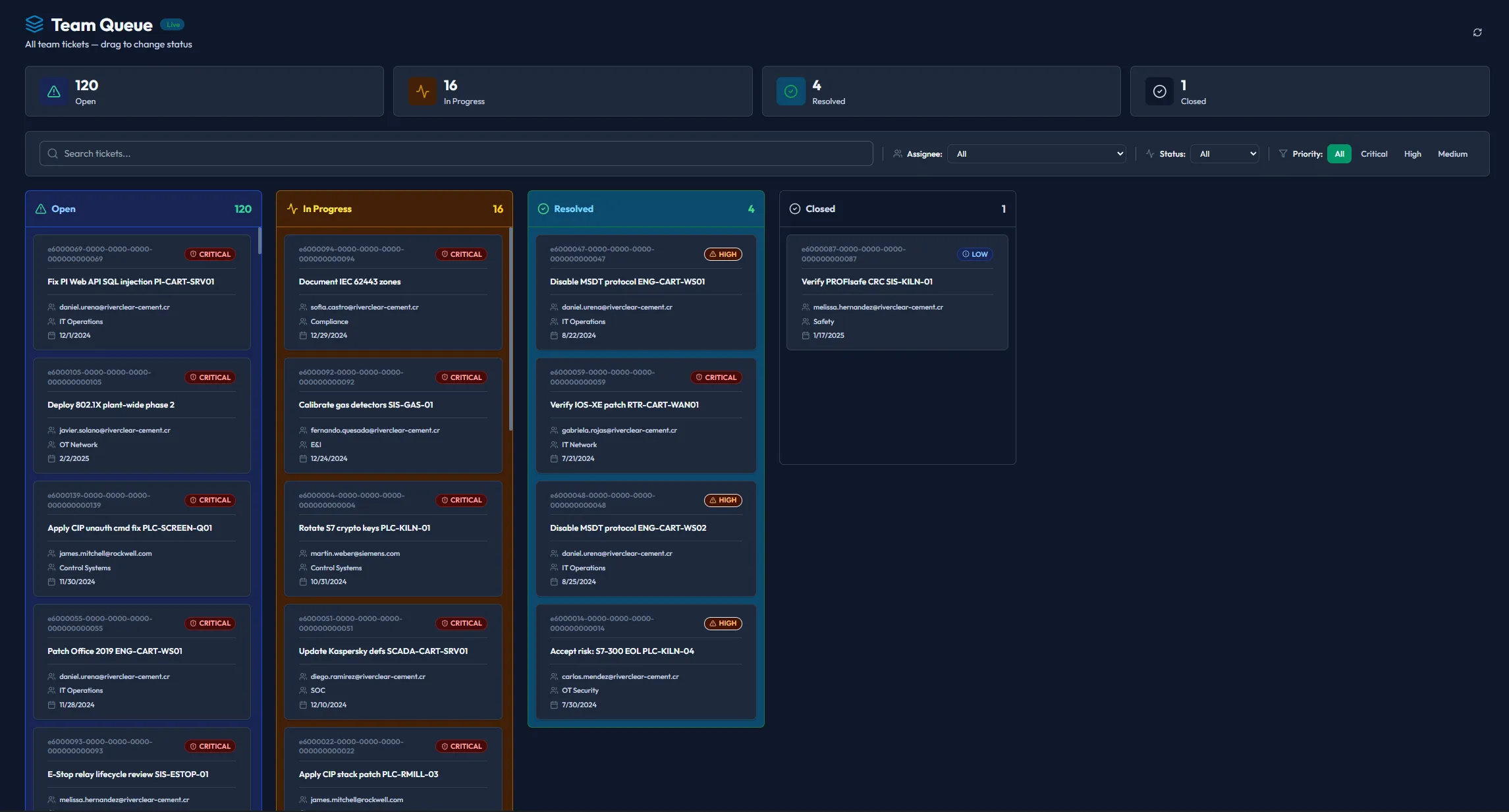
Intelligent Team Queue
Dynamic task distribution based on analyst expertise and current bandwidth. Piscium's workflow engine ensures high-priority remediation tasks never sit idle, providing real-time visibility into SOC productivity.
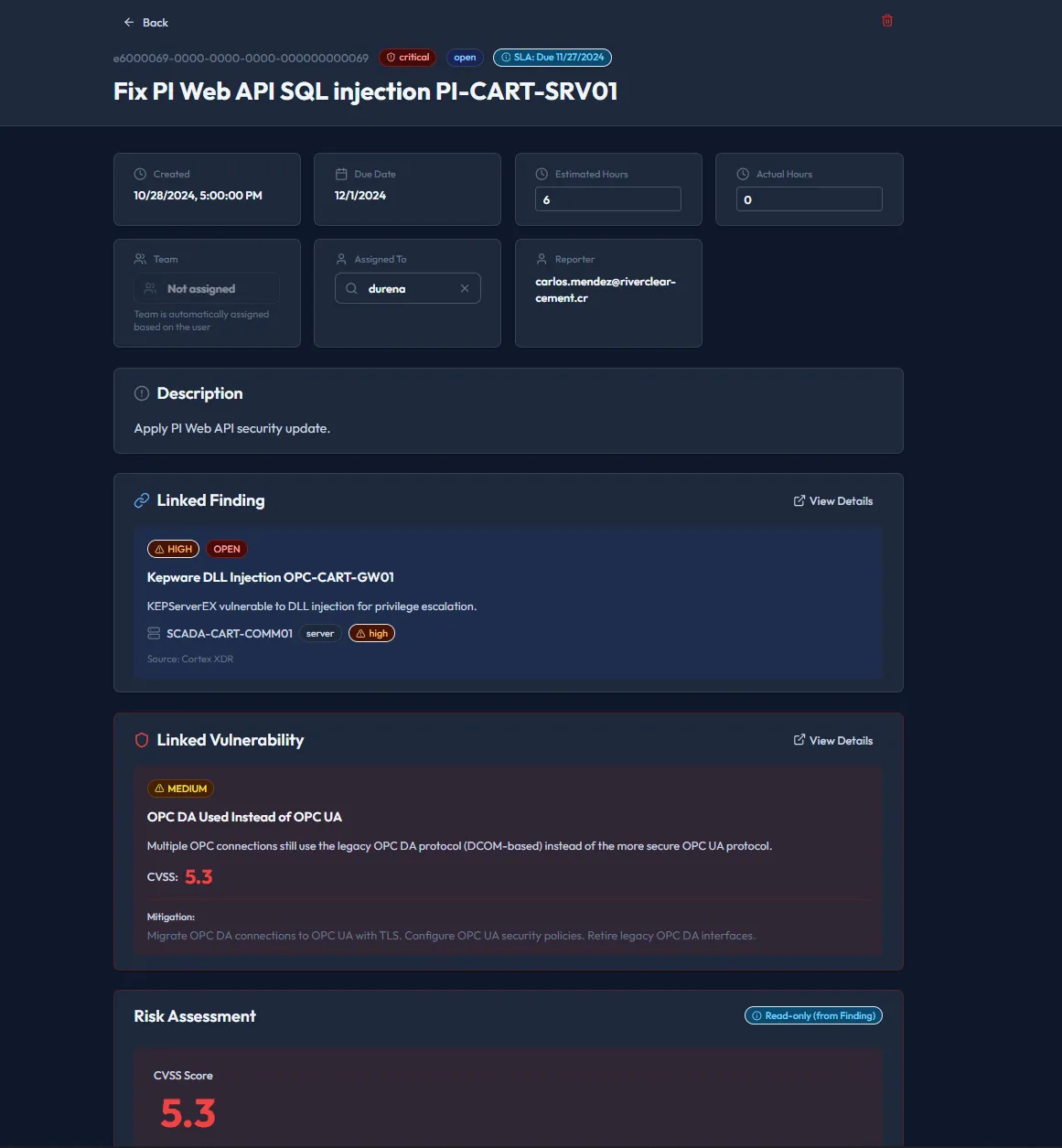
Deep Remediation Detail
Go beyond the alert. Every ticket contains a complete audit trail, integrated playbooks, and direct synchronization with IT service management platforms like Jira and ServiceNow.
- Bi-directional ITSM Synchronization
- Automated Evidence Collection
- Collaborative Analyst Commenting
Unified Security Operations
Converging SIEM, SOAR, and XDR into a single high-performance canvas. Designed for teams that demand clarity over complexity.
Intelligent Ingestion
Hyper-scale data normalization that prioritizes signals over noise. Integrated at the architectural level to reduce latency in detection.
Autonomous Response
Dynamic playbooks that evolve based on behavioral patterns. Reduce human intervention for routine remediation by up to 85%.
Global Context
Enrich every alert with real-time threat intelligence from the Piscium network, providing instant "why" and "how".
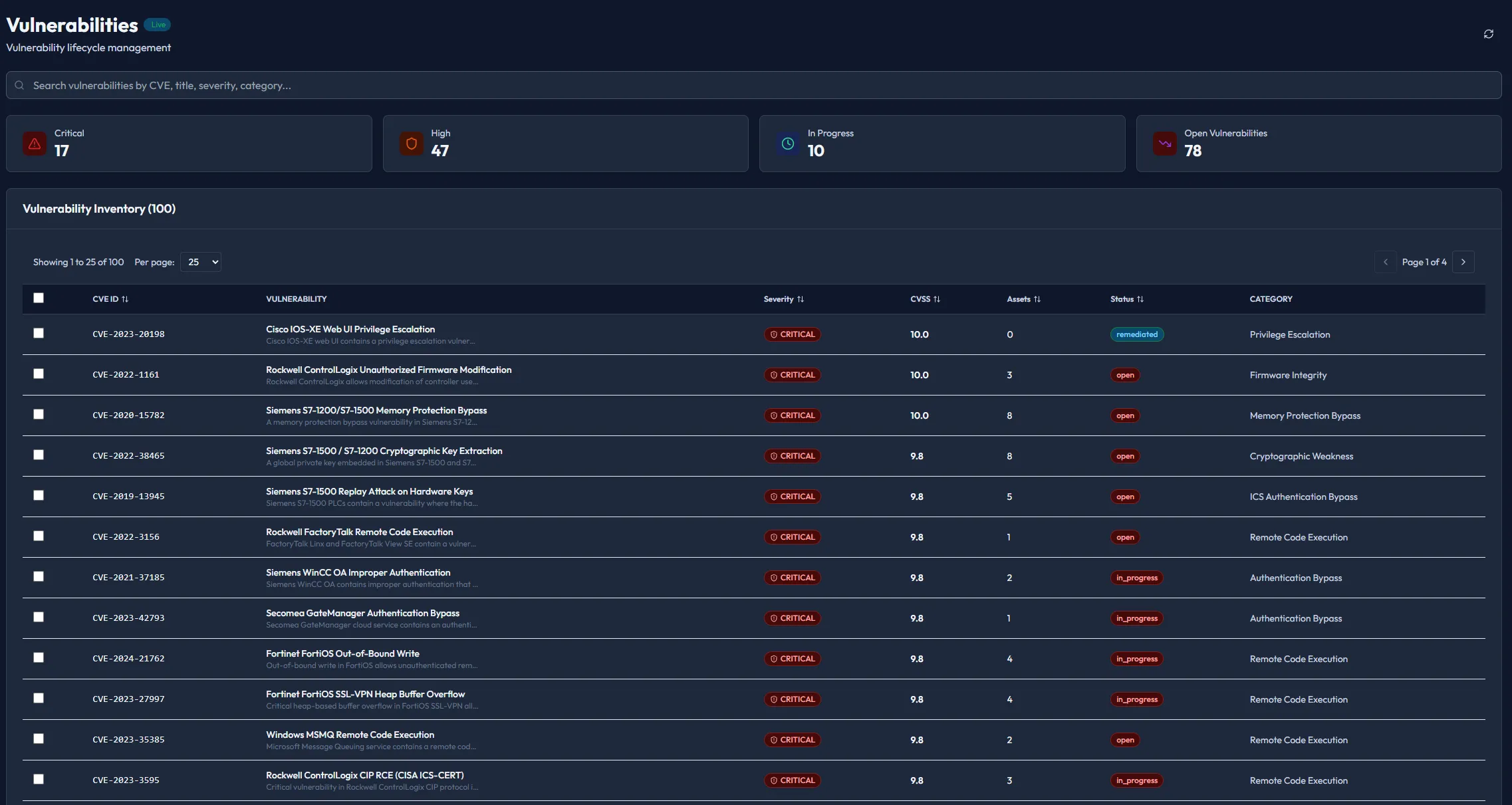
Continuous Exposure Management
Security isn't a point-in-time check. It's a living architecture. Piscium maps your attack surface in real-time.
Vulnerability Prioritization
We go beyond CVSS scores. Piscium calculates risk based on exploitability, asset criticality, and active threats in your environment.
Attack Path Analysis
Visualize how attackers navigate your network. Proactively sever connections before they are exploited.
Shadow IT Discovery
Identify unmanaged cloud resources and misconfigurations instantly across AWS, Azure, and GCP.
Operational Efficiency at Scale
Stop hiring your way out of security debt. Piscium empowers smaller teams to perform like global SOC giants through systemic automation and precision architecture.
Team Productivity Lift
Automated triage frees analysts for hunting.
Faster Response Cycles
Integrated workflows eliminate tool-switching.
Systemic Architecture
Ready to Architect Your Defense?
Join 500+ security teams who have moved from reactive fire-fighting to precision-orchestrated operations.